[lang:en] 
[lang:de]? See previous post.
On September 23, TMC DACH met for its third Threat Modeling After-Work Event. This was our sixth event overall.
As always with the Threat Modeling After-Work format, a toolbox met a playground.
This evening discussed the Fortunately/Unfortunately of End-to-End Encryption and followed this agenda:
First, we discussed the method. Then we discussed E2EE. Then we applied the method to E2EE in an interactive exercise.
The material
All slides (![]() German):
German):
Whitepaper “Fast, Cheap and Good”, that among other things introduces Fortunately/Unfortunately:
Discussion of advantages and disadvantages of the method, introduction of Fortunately/Unfortunately Forests as written tree structures:
New project about E2EE Adoption Challenges as Fortunately/Unfortunately Forest:
Launch post in this forum:
Tools for better privacy:
privacypack.org / prism-break.org / privacytools.io
Fortunately / Unfortunately
Fortunately / Unfortunately was introduced by @adamshostack .
The method alternates between “Unfortunately…” and “Fortunately…” sentences. Anyone discussing the security of a system in this way is applying a threat modeling method. The written conversation is a threat model.
The simple introduction example talks about how Fortunately threat modeling can introduce more secure systems, but Unfortunately threat modeling is complex, but Fortunately there’s lightweight methods - introducing the back and forth typical for Fortunately / Unfortunately conversations.
After the small example it was tested on an everyday interactive example (“Unfortunately, I’m totally stressed out”).
Jan provided insights into how he used the method in a technical context. This clearly demonstrated both its practicality and one of its advantages: that organizational issues can also be discussed effectively - e.g., significant costs.
A reference to the Fortunately/Unfortunately of Fortunately/Unfortunately project briefly mentioned some of the advantages and disadvantages of the method. There was also a discussion of how the method can be used orally and flatly or in writing as a tree structure.
End-to-end Encryption (E2EE)
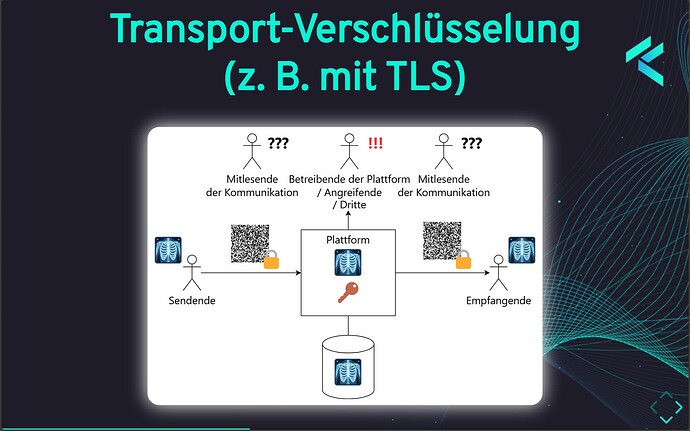
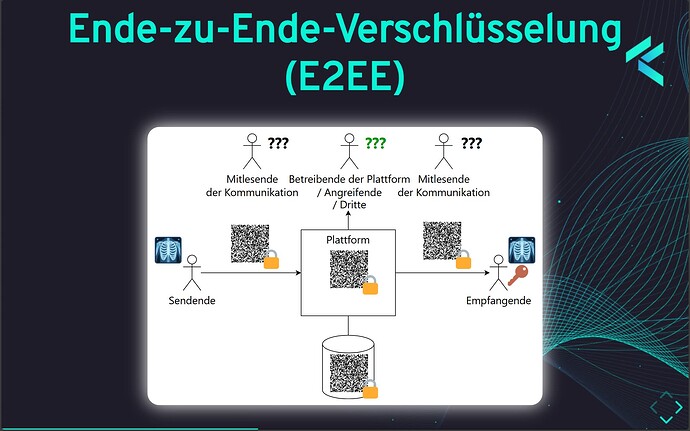
A brief introduction to end-to-end encryption primarily highlighted the difference between transport encryption and end-to-end encryption and pointed out the advantage that E2EE prevents service providers, attackers, and third parties from reading the data.
Then a little more context was provided and reference was made to collections that recommend tools with better data protection features. These often include E2EE as well.
Fortunately / Unfortunately of E2EE
The interactive part began with the question of the evening:
If E2EE is so great, why does “nobody” build E2EE solutions?
We approached the question step by step by answering different “Unfortunately…” openings on the topic. The original plan was to split the group. However, the conversation went so smoothly that we spontaneously decided to stay together.
The openings discussed were:
-
 Unfortunately, everything will break with the next version and all secrets will be revealed.
Unfortunately, everything will break with the next version and all secrets will be revealed. -
 Unfortunately, providers do not see themselves as a threat actor, so they will not defend against themselves.
Unfortunately, providers do not see themselves as a threat actor, so they will not defend against themselves. -
 Unfortunately, users have no idea what E2EE is and what it is used for.
Unfortunately, users have no idea what E2EE is and what it is used for. -
 Unfortunately, potential users still don’t trust the providers.
Unfortunately, potential users still don’t trust the providers. -
 Unfortunately, the operators will then no longer be able to access the data.
Unfortunately, the operators will then no longer be able to access the data. -
 Fortunately, our product will soon have E2EE.
Fortunately, our product will soon have E2EE.
Participants saw a screen like this - you can see the final collection for the opening “![]() Fortunately, our product will soon have E2EE” (German)
Fortunately, our product will soon have E2EE” (German)
Exchange
Then there was an opportunity to discuss the method: The method was certainly surprising and was perceived as refreshingly new and simple. Doubts arose as to whether it could meet the requirements of formal, complete threat modeling and whether it could be applied to specific technical considerations in sufficient depth. However, it was appreciated that, depending on the occasion, it could provide an uncomplicated introduction to the topic. Jan was able to report again on how he had processed the results at the time: After the lightweight “unfortunately/fortunately” phase, they had identified action points and then formulated them more formally.
Release party
There was cause for celebration when Hendrik published his project on the Fortunately / Unfortunately of End-to-End Encryption, which is now available at threat-modeling.net. Contributors are welcome! Threat Modeling of E2EE Adoption
Results
Here is the raw results in German language.
Threat-Modeling-Results-de.txt (6.7 KB)
Next Event: International Threat Model Together Day!
Our next event is the international Threat Model Together Day, where we will have the same event three times, so we can cover the whole world! Join the EMEA sesssion! TMC DACH is already looking forward to meet their international friends…